Endpoint Protection
Network and data security management to keep your business available and secure 24/7.
Managed network perimeter protection supported. Equipment, Software, and monitoring included.
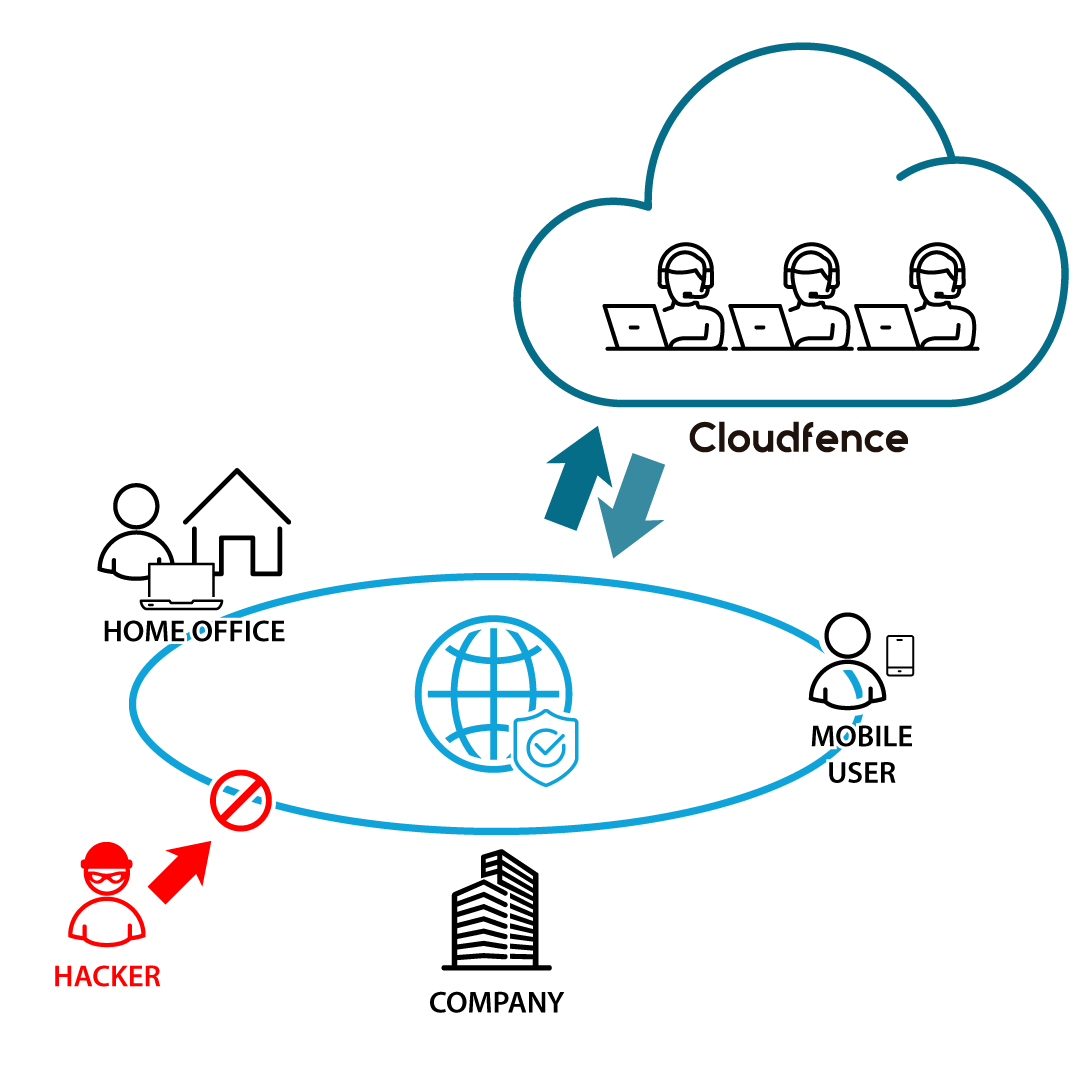
How does it work
Advantages of Endpoint Protection
Cost control
Investment in the definition of the environment, licenses and training are tied to a specific need at the moment
of subscription and grow according to the client’s use demand, without unpleasant surprises in the future
More Security
Security management by professionals specialized in the technology used, reducing policy execution time and increasing the level of network protection
More Availability
24/7 monitoring against attempted attacks and other events, preventing unplanned downtime
Greater Integration
Connect offices to remote users and cloud environments transparently and securely

